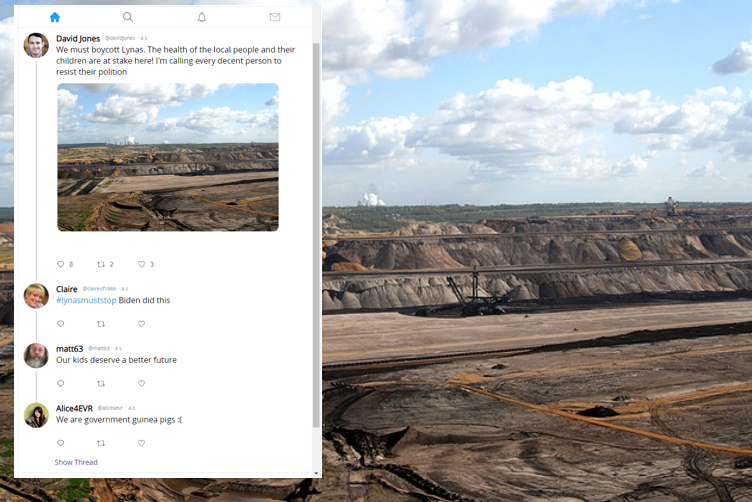
Threat intelligence company Mandiant published this report on an influence campaign known as DRAGONBRIDGE which used fake accounts to try to stop or stifle the mining of rare earth minerals by microtargeting local populations and calling them to protest.
How would Conducttr simulate this activity to exercise threat analysts or communicators?
Here’s the steps:
- Research: Read the article and highlight the building blocks
- Foundations: Build the personas and find rich media assets
- Audiences: Turn personas into audiences using Pattern of Life
- Sequencing: Write the Master Events List(s)
Research: Breaking down the components
All good stories start with personal experience or good research. We have the Mandiant report so the first task is to read through and gather the following:
- Places – we’ll use this to geotag our personas and also create local media
- People (A3E) – articles highlight key individuals & organisations (Actors & Adversaries), the populations affected (Audiences). It’s here we’ll put personas into Factions
- Narratives – what the Factions saying about each other and what hashtags & lexicons are they using?
- Timeline – what are the key milestones in the build up of the influence activity (when, where, who, how)
- History – what past information is needed to build credibility into the information environment? Is there evidence of information laundering we need to build in?
- Rich media – what images and videos will we need?
At this point you might delegate the work to collaborators and have colleagues working in parallel:
- Scenario designer 1 : Personas
- Scenario designer 2 : Timeline
- Scenario designer 3 : Rich media
- Scenario designer 4 : Content creation
Foundations: Building personas
Now we get to work creating the personas. If libraries already exist then we can reuse what we have, potentially cloning a library and moving the personas to the desired geolocation.
Persona building with Conducttr is described here https://conducttr.helpdocs.com/personas2/personas
It’s during this stage that we should use a disposition chart (shade shift diagram) to understand the position of audience towards the training audience. This will pay off later because our pattern of life will be more authentic and that means feedback to the training audience will be more credible: https://conducttr.helpdocs.com/personas2/measurement-of-messaging-effects
Use bulk edit to shape the personas into advocates and detractors https://conducttr.helpdocs.com/personas2/bulk-persona-editing
Audiences: Pattern of Life
Conducttr’s Pattern of Life feature allows you to script expected responses from target audiences. These are then played on demand either when prompted by the master events list or in response to the training audience actions or inaction.
https://conducttr.helpdocs.com/pol-overview/pattern-of-life
It’s important during scripting that the content you write matches the lexicon and hashtags identified during research and that the different audiences have authentic dispositions. Paying attention to these details will ensure that our simulated social media listening features like Social Watch and Pulse produce realistic insights.
You might consider using Conducttr’s smartwords to create variables to allow yourself to easily change hashtags during testing. They’ll also allow you to more quickly reuse libraries in the future.
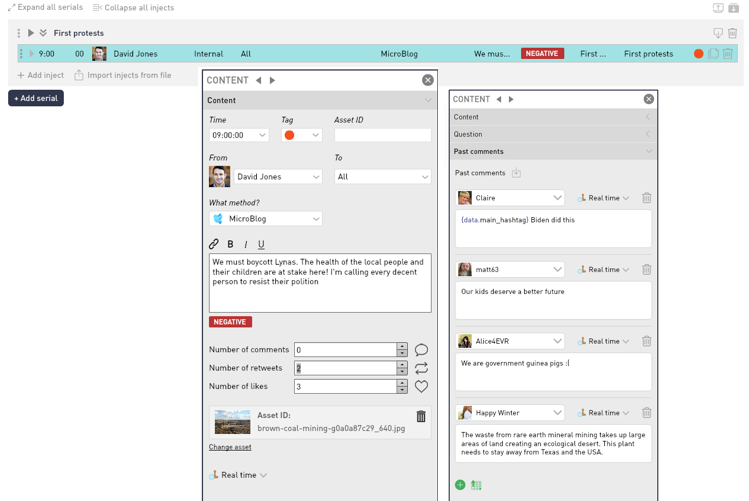
Sequencing: Write the Master Events List(s)
This should now be the easiest part to build and you could even have someone unfamiliar with Conducttr to do this part in Excel and import into the scenario editor for you to polish.
A well written research paper will usually give a good account of the timeline but you ought to consider where in the timeline your exercise starts. Our recommendation is to pick something close to an inciting incident which is the reason for the exercise. All content prior to this date can be written as “historic content” and will appear in the information environment at the start state without needing to be published during the exercise – making the exercise period more engaging and the environment more credible.
Similarly chains of comments to posts and engagement can be published as a block or using Conducttr’s “spoof engagement” feature develop over time. Your choice here depends on the length of the exercise and training objectives.
Bottom line
When you get some excellent research, don’t waste time any time – get building your simulation and rehearse!